Whenever a new product is released, feedback is given by the public. They are tasked with figuring out the good and bad points of said product. The surest way to get good feedback is to not release the product late. This means not to release a product after its launch date.
Now, every application and product can have loopholes or dangerous side effects. It seems that Apple’s AirDrop also has vulnerability inside it. While this may not be entirely surprising information, it is certainly alarming for routine AirDrop users. No one wants to have an open dangerous anomaly in their phone system.

AirDrop is an application that has been made specifically for Apple users. If you have an Apple product, be it the mac or the iPhone, AirDrop is a must built-in feature. It allows IOS users to transfer and share files with each other at great speed.
AirDrop makes use of Wi-Fi and Bluetooth. It uses encrypted transfer techniques to make sure the files themselves aren’t compromised. However, there is a vulnerability present that can compromise the user’s device or their own personal information.
AirDrop Exposure:
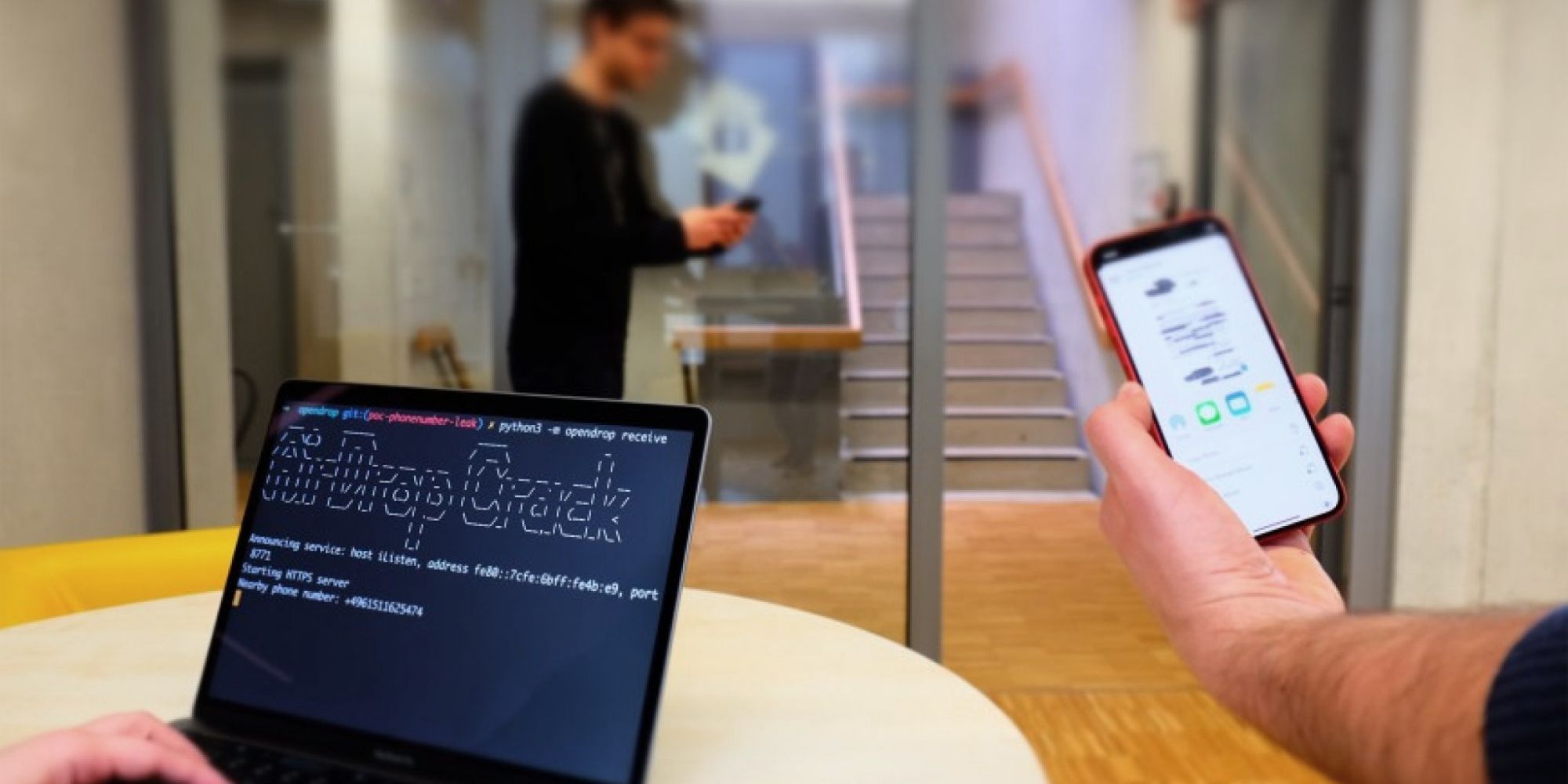
The application itself makes use of hash functions when transferring files. During this, the hash functions exchange mobile numbers and email addresses of the user. Anyone who has set their file receiving settings to ‘Everyone’ is highly at risk. Additionally, if your share sheet is open when you are looking to connect with other devices, you are also at risk.
While the number and email are encrypted, a hacker close to the device, with Wi-Fi, can decrypt those encryptions. This means that you have to be quite careful when you use AirDrop. You never know when someone may be passing nearby with malicious intentions.
This exposure in AirDrop’s system was reported to Apple back in 2019. However, Apple did not respond or reply to the query and thus, it went unnoticed. Now, it seems to have sprung back up.
Safety First:
There are two possible scenarios under which a phone’s data can be leaked. The first one is, you keep your share sheet out in the open. The second is the hacker keeps their share sheet out in the open.
The second one is less likely to get a catch because the base is a lot smaller. So, the next time you use AirDrop, be very careful on which info to keep public and which to keep private. Additionally, always keep a strict eye around you as walls have ears too.
You never know when a simple song or photo exchange may end up costing you your user data. Finally, we hope that Apple finds a way to close this loophole, of sorts. If you wish to understand more about this problem and its solution, there is a research paper present online. It discusses the concept of ‘PrivateDrop’.
Stay tuned for more from Brandsynario!